Overview
Your security team has recommended enforcing TLS 1.2 or 1.3 on your Lyris LM server(s) and you would like to know if this is possible and how to implement it. Note that this works for HTTPS only.
Solution
Important for ListManager 12.4.11 and later
Starting with ListManager 12.4.11, HTTPS traffic supports TLS 1.3 natively. In standard deployments, ListManager can support modern SSL/TLS security, including an A+ SSL/TLS rating in typical configurations, without requiring an NGINX reverse proxy solely for transport hardening.
This article remains relevant if you still want to place NGINX in front of ListManager for architectural reasons such as centralized redirect handling, proxy-based routing, or environment-specific network controls.
If you prefer a lighter-weight external TLS termination approach for single-domain environments, see the Enforcing TLS 1.2 or 1.3 in Lyris LM using Stunnel article.
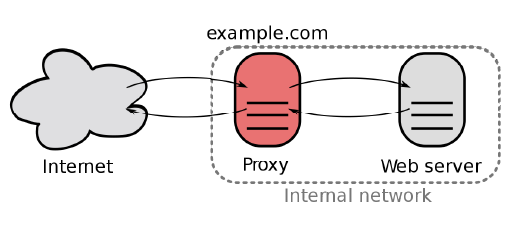
What is the reverse proxy?
A reverse proxy server is a type of proxy server that typically sits behind the firewall in a private network and directs client requests to the appropriate backend server. A reverse proxy provides an additional level of abstraction and control to ensure the smooth flow of network traffic between clients and servers, including security, availability, performance, and traffic shaping.
Why do we need it?
A reverse proxy may still be useful when your organization wants a separate front-end layer for redirect handling, routing, or environment-specific network controls. It is no longer required solely to provide modern HTTPS transport security in ListManager 12.4.11 and later.
How does it work?
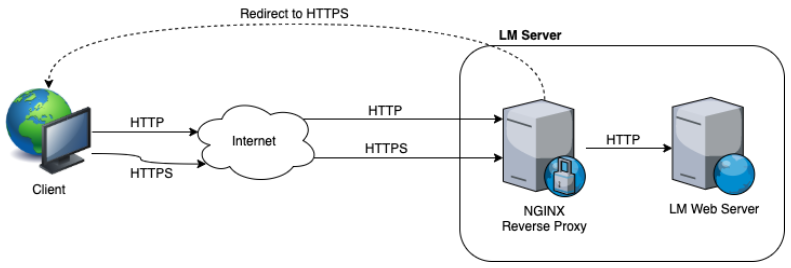
The diagram below illustrates how NGINX can be placed in front of the LM web server, redirecting HTTP traffic to HTTPS while proxying requests to the LM HTTP service. This remains an optional deployment pattern for customers who want a reverse proxy layer in front of ListManager.
In this design, NGINX listens on HTTP (TCP 80) and HTTPS (TCP 443) and mediates connections to the LM HTTP server on TCP 8080 when both services run on the same server.
Testing
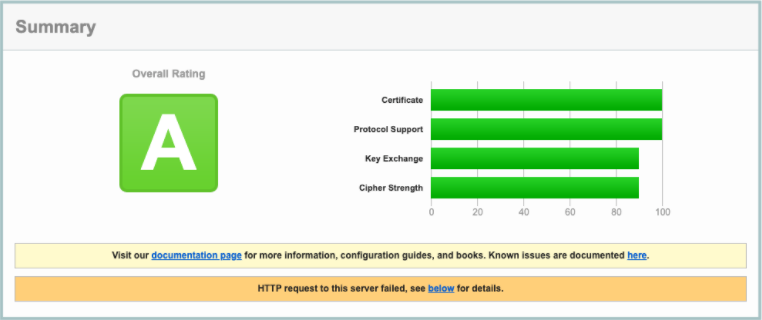
After implementing the NGINX reverse proxy, you can validate the resulting HTTPS configuration with your preferred SSL/TLS assessment tool.

Priyanka Bhotika
Comments